Featured
Table of Contents
- – 10 Best Vpn Services Of 2023
- – How Does A Vpn Work?
- – What Is A Vpn And Why You May Need One
- – Vpn - Definition By Acronymfinder
- – What Is Vpn And How Does It Work?
- – What Is A Vpn? How It Works & Why Online Sec...
- – What You Need To Know About Vpns
- – What Does Vpn Stand For? Why People Using Vpn
- – Virtual Private Networks (Vpns) - Ncsc.gov.uk
- – Everything You Need To Know About Vpns For T...
- – Vpn Meanings - What Does Vpn Stand For?
- – What Is A Vpn & How Does It Work?
10 Best Vpn Services Of 2023
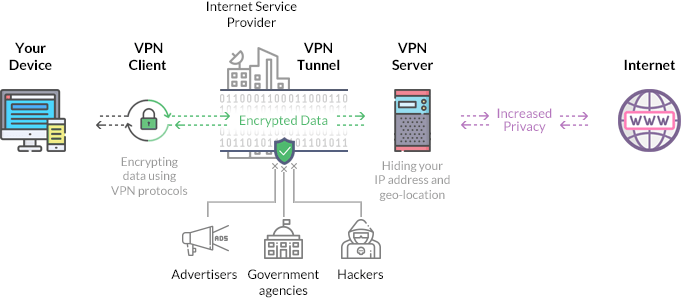
Anyone on the same network will not be able to see what a VPN user is doing. This makes VPNs a go-to tool for online privacy. A VPN uses tunneling procedures to secure data at the sending end and decrypts it at the receiving end. The stemming and receiving network addresses are likewise secured to offer better security for online activities.
The VPN client is not obvious to the end user unless it creates efficiency issues. By utilizing a VPN tunnel, a user's gadget will link to another network, concealing its IP address and encrypting the data. This is what will hide private information from assailants or others wanting to gain access to an individual's activities.
VPNs associate a user's search history with the VPN server's IP address. VPN services will have servers situated in various geographical locations, so it will appear like the user could be from any one of those places. VPNs can affect performance in many methods, like the speed of users' web connections, the procedure types a VPN provider can utilize and the kind of encryption used.
How Does A Vpn Work?
If the VPN connection is interfered with, the kill switch will automatically detach the device from the internet to get rid of the possibility of IP address direct exposure. There are two types of kill switches: avoid gadgets from connecting to unsafe networks when the gadget is linked to the VPN.
They keep the device from connecting to non-VPN connections even while disconnected from the VPN server. VPNs are used for virtual personal privacy by both normal internet users and organizations.
When surfing the web, a web user could have info accessed by an opponent, consisting of searching practices or IP address. If privacy is an issue, a VPN can supply users with peace of mind. Encryption, anonymity and the capability to navigate geographically blocked content is what most users discover important in a VPN.
What Is A Vpn And Why You May Need One
The obstacles of utilizing a VPN, nevertheless, consist of the following: Not all devices may support a VPN. VPNs do not secure versus every hazard.
Network administrators have numerous options when it comes to releasing a VPN that consist of the following. The entrance requires the gadget to confirm its identity before giving access to internal network resources.
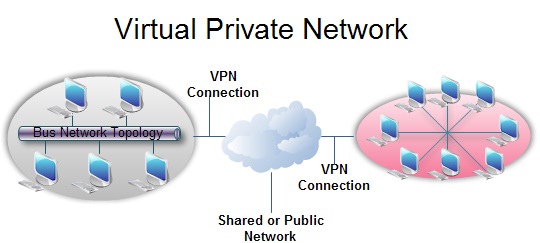
End-node devices in the remote location do not need VPN clients because the gateway handles the connection. Most site-to-site VPNs connecting over the web usage IPsec.
Vpn - Definition By Acronymfinder
resource that talks about what vpns are
In a mobile VPN, the server still sits at the edge of the company's network, allowing safe and secure tunneled access by verified, licensed clients. Mobile VPN tunnels are not tied to physical IP addresses. Instead, each tunnel is bound to a rational IP address. That logical IP address remains to the mobile device.
Hardware VPNs use a number of benefits over software-based VPNs. A hardware VPN is more costly than a software-based one. Since of the cost, hardware VPNs are more viable for larger services.
Paid vendor choices tend to be suggested more typically than free ones. Some VPNvendors, amongst numerous, consist of the following: consists of a strong collection of security functions with a large collection of servers. Nord, VPN has functions such as Tor browser connections for anonymous web surfing, while maintaining a strong position on customer privacy.
What Is Vpn And How Does It Work?
It does not offer excessive in terms of additional functions and personal privacy tools, however. Still, it is generally thought about a good VPN service. is a VPN service with a large and varied set of distributed servers. It has strong privacy and info practices concentrated on security and uses additional features such as split tunneling.
VPNs are legal in the United States, however users and companies ought to inspect if they are legal in particular nations. Many VPNs provide very comparable technologies, so it can be hard to choose which VPN will work best. Paid VPN services tend to be more trusted and include more security features.
Around 2017, web users in the United States discovered that ISPs could gather and sell their browsing history, and net neutrality became an idea citizens needed to defend-- and successfully lost. A bill was gone by the U.S. Legislature in 2019 to bring back net neutrality, but was eventually obstructed by the Senate.
What Is A Vpn? How It Works & Why Online Security Matters
With this understanding, using VPNs ended up being a more legitimate need for people.
Extranet-based site-to-site In the context of site-to-site configurations, the terms and are utilized to describe 2 different usage cases. An intranet site-to-site VPN explains a setup where the sites connected by the VPN belong to the exact same company, whereas an extranet site-to-site VPN joins websites belonging to multiple companies.
An SSL VPN can link from locations where IPsec runs into problem [] with Network Address Translation and firewall guidelines. Datagram Transport Layer Security (DTLS) used in Cisco Any, Link VPN and in Open, Connect VPN to fix the problems TLS has with tunneling over TCP (SSL/TLS are TCP-based, and tunneling TCP over TCP can cause big hold-ups and connection terminates).
What You Need To Know About Vpns
Multiprotocol Label Switching (MPLS) performance blurs the L2-L3 identity. [] 4026 generalized the following terms to cover L2 MPLS VPNs and L3 (BGP) VPNs, but they were presented in 2547. Client (C) gadgets A device that is within a customer's network and not straight connected to the service supplier's network. C gadgets are not familiar with the VPN.
Sometimes it is just a separation point between supplier and customer obligation. Other companies permit consumers to configure it. Provider edge gadget (PE) A device, or set of devices, at the edge of the service provider network that connects to consumer networks through CE gadgets and presents the service provider's view of the client site.
Service provider device (P) A device that operates inside the company's core network and does not straight user interface to any consumer endpoint. It might, for instance, provide routing for lots of provider-operated tunnels that come from various clients' PPVPNs. While the P device is a key part of carrying out PPVPNs, it is not itself VPN-aware and does not preserve VPN state.
What Does Vpn Stand For? Why People Using Vpn
From a user viewpoint, a VPLS makes it possible to adjoin numerous LAN sections over a packet-switched, or optical, company core, a core transparent to the user, making the remote LAN sectors behave as one single LAN.
PW is comparable to VPLS, but it can offer various L2 procedures at both ends. In contrast, when intending to offer the look of a LAN adjoining between two or more areas, the Virtual Private LAN service or IPLS would be appropriate.
This area talks about the main architectures for PPVPNs, one where the PE disambiguates replicate addresses in a single routing circumstances, and the other, virtual router, in which the PE includes a virtual router circumstances per VPN. The former technique, and its versions, have actually gotten the most attention. One of the obstacles of PPVPNs includes various customers using the same address area, specifically the IPv4 private address space.
Virtual Private Networks (Vpns) - Ncsc.gov.uk
A restriction of traditional VPNs is that they are point-to-point connections and do not tend to support broadcast domains; therefore, interaction, software, and networking, which are based upon layer 2 and broadcast packages, such as Web, BIOS used in Windows networking, may not be totally supported as on a regional area network. A VPN does not make one's Web "personal". Users can still be tracked through tracking cookies and device fingerprinting, even if the user's IP address is hidden. A VPN can log the user's traffic, however this depends on the VPN service provider. A VPN does not make the user unsusceptible to hackers.
Before we dive directly into the inner operations of a VPN, it is a good concept to familiarize yourself with the fundamentals of what a VPN is and what it does. The acronym VPN represents Virtual Private Network. As the name suggests, it supplies users with a virtual network that is private so that they can link to the web in such a way that is safe and secure.
We highly suggest you read this article for a more in-depth explanation of a what a VPN is before you read this one, but here's a short primer in any case. How exactly does a VPN do that? A VPN works by routing your device's web connection through your chosen VPN's personal server rather than your internet service provider (ISP) so that when your data is transferred to the internet, it comes from the VPN rather than your computer system.
Everything You Need To Know About Vpns For Travel In 2023
This implies that your information is transformed into an unreadable code as it travels in between your computer system and the server of the VPN.Your device is now seen as being on the exact same local network as your VPN. So your IP address will really be the IP address of among your VPN Company's servers.
It utilizes an application that develops an encrypted connection to the personal network that you can then make use of to connect to the web at big. Some VPNs work as an internet browser add-on. There are a wide variety of add-ons you can set up to internet browsers like Google Chrome or Firefox, while Opera features a built-in VPN.
This is perfect if you have several gadgets you want to secure as it will safeguard every gadget linked to the router, conserving you needing to install the VPN separately. You'll only need to sign in when; your router will always be linked to your VPN.Connecting your router to a VPN isn't as hard as you may think.
Vpn Meanings - What Does Vpn Stand For?
The most hassle-free type of router to get is one that is developed to support VPNs right away, without you having to do anything more technical that entering your VPN details. These routers can be somewhat more pricey than routine routers, however the benefit deserves it. Organizations often utilize a remote-access VPN for employees who work remotely.
This is a custom-created option that needs individualized development and heavy IT resources. We've discussed how a VPN works and some various ways to execute a VPN, but why precisely should you utilize a VPN? A lot of people will most likely concur that the basic tenets of a VPN are an advantage.
That stated, lots of people delay getting a VPN, considering it inessential or, worse, unnecessary. An excellent method of illustrating the need of a VPN is to show simply how exposed you are when your web connection is not encrypted.
What Is A Vpn & How Does It Work?
By not utilizing a VPN, you're not rather shouting your most delicate info from the rooftops, but it is a little like leaving your front door open with your personal information easily laid out on a table right inside the door. Perhaps you have excellent, truthful next-door neighbors that will not be available in and take what is important.
Table of Contents
- – 10 Best Vpn Services Of 2023
- – How Does A Vpn Work?
- – What Is A Vpn And Why You May Need One
- – Vpn - Definition By Acronymfinder
- – What Is Vpn And How Does It Work?
- – What Is A Vpn? How It Works & Why Online Sec...
- – What You Need To Know About Vpns
- – What Does Vpn Stand For? Why People Using Vpn
- – Virtual Private Networks (Vpns) - Ncsc.gov.uk
- – Everything You Need To Know About Vpns For T...
- – Vpn Meanings - What Does Vpn Stand For?
- – What Is A Vpn & How Does It Work?
Latest Posts
Best Vpn Services 2023: Top Picks For Speed, Price, Privacy ...
8 Best Vpns For Small Businesses In Jul 2023
The Best Vpn For Business In 2023: Top 8 Corporate ...
More
Latest Posts
Best Vpn Services 2023: Top Picks For Speed, Price, Privacy ...
8 Best Vpns For Small Businesses In Jul 2023
The Best Vpn For Business In 2023: Top 8 Corporate ...